- Crypto money launderers are attacking their own trades.
- Doing so helps them make illicit funds look clean.
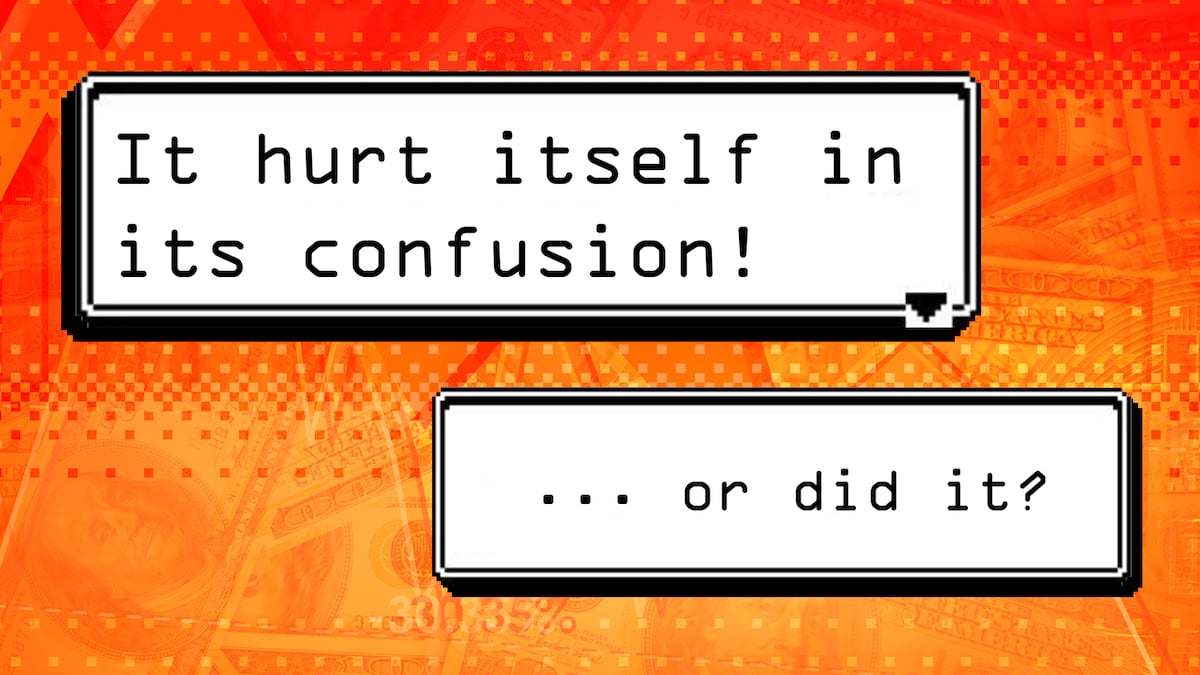
Crypto thieves are pretending to be inexperienced traders — losing thousands of dollars on purpose — in a new method of laundering illicit funds.
That’s according to two crypto security experts, who told DL News that the tactic is being deployed by hackers.
The method works like this: Launderers engineer token swaps that are designed to fall victim to trading bots. However, instead of letting other bots take advantage, the launderers run their own bots to profit from the trades.
On the surface, it looks like an inexperienced trader losing money.
But in reality, the bad trades are turning the illicit funds tied to blacklisted wallets into clean funds which, to most onlookers, appear to be trading bot profits unconnected to the illicit funds.
“We believe this is an evolving strategy to bypass detection and enforcement mechanisms,” Hakan Unal, senior security operation center lead at crypto security firm Cyvers, told DL News.
Centralised crypto exchanges like Binance and Coinbase are locked in a never-ending game of cat and mouse with some of the world’s top crypto criminals.
Money launderers are continuously looking for ways to bypass these exchanges’ anti-money laundering detection.
Multi-step process
The trades have all the characteristics associated with money laundering, Yehor Ruditsya, a security researcher at blockchain security firm Hacken, told DL News.
Ruditsya identified multiple transactions from wallets which he said raised “significant red flags” because they sent funds through FixedFloat and ChangeNow, two crypto mixers popular with money launderers.
The scheme takes advantage of Circle’s USDC and Tether’s USDT stablecoins through a multi-step process.
First, several wallets deposit and withdraw funds to DeFi lending protocol Aave. After withdrawing funds from Aave, the launderers add the stablecoins to a trading pool on decentralised exchange Uniswap.
Usually, stablecoins like USDC and USDT trade at close to the same value. After all, they are both meant to closely track the value of the dollar.
However, launderers set up the Uniswap trading pools so that when they use them, a trading bot they control can attack the trades.
In one example, the launderers swapped $90,000 USDC for just $2,300 USDT — an $87,700 loss. While the wallet that submitted the transaction loses money, that amount lost gets picked up by the launderer’s trading bot as an arbitrage profit.
Ruditsya said he identified six of these highly uneven trades using the same trading pool within just five minutes of each other, indicating organised activity.
However, others question whether such activity really is part of an elaborate money laundering scheme.
After the publication of this story, Reid Yager, head of policy at Flashbots, told DL News that a well-known trading bot was taking advantage of the vulnerable trades.
If it was money laundering, Yager said, the launderer’s bot would not have been able to guarantee they would win the opportunity to attack the vulnerable trade.
Hacken maintains that its analysis of transactions and the scheme is correct.
Sandwich attack
Trading bots take advantage of a blockchain-specific arbitrage technique called maximal extractable value, or MEV.
Bots pay to reorganise onchain trades in the most profitable way. Doing so helps keep the prices of assets on decentralised exchanges accurate. But it can also negatively affect traders.
Often, bots can orchestrate so-called sandwich attacks. Such attacks start when a bot sees a trader place a big order for a specific token.
The bot then buys up a large amount of that token ahead of the trader, pushing up its price.
After the trader has had their order filled at the higher price, the bot sells the tokens at the even higher price, profiting at the trader’s expense.
It is these sandwich attacks that crypto criminals are potentially replicating to launder funds.
More methods
It’s not just sandwich attacks that launderers are using to obscure funds, Cyvers' Unal said.
Another common tactic, he said, involves piling money into trading pools of obscure or low-value tokens and then removing it to create the appearance of legitimate funds.
Unal highlighted one instance where Cyvers tracked an address belonging to North Korean hackers Lazarus Group that had been engaging in this method, using a token called WAFF and Tether’s USDT stablecoin.
The reason Lazarus used this method is to evade detection at crypto exchange OKX, Taylor Monahan, the lead security researcher at the crypto wallet MetaMask, told DL News.
North Korean hackers used OKX’s web3 service to launder $100 million in stolen crypto from last month’s Bybit hack.
As a result, Tether blocked the Uniswap pool associated with the WAFF token, Unal said.
Tether did not immediately respond to a request for comment.
Correction, March 28: This article previously quoted Cyvers' Unal as implying that North Korean hackers, the Lazarus Group, used the MEV laundering technique. Cyvers later clarified that North Koreans are not known to use this technique but employ a different method to bypass AML filters on OKX. The story has been corrected.
Commentary from Taylor Monahan, the lead security researcher at crypto wallet MetaMask, on this new method has also been added.
The article has also been updated to include comments from Reid Yager, head of policy at Flashbots, questioning the assumptions about the MEV laundering technique and to note that Hacken stands by its analysis.
Tim Craig is DL News’ Edinburgh-based DeFi Correspondent. Reach out with tips at tim@dlnews.com.